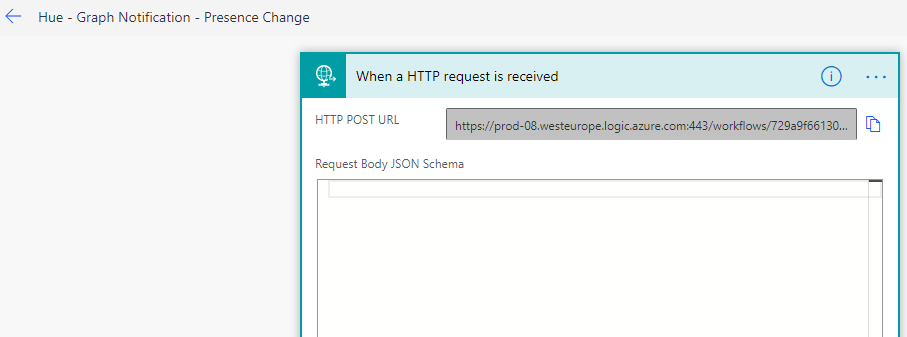
Azure Logic Apps are great for creating workflows for your IT automation scenarios. Logic App workflows can be triggered using a variety of sources and events, including schedules, but a popular trigger is using a HTTP trigger for starting the Logic App workflow interactively or on-demand from outside the Logic App.
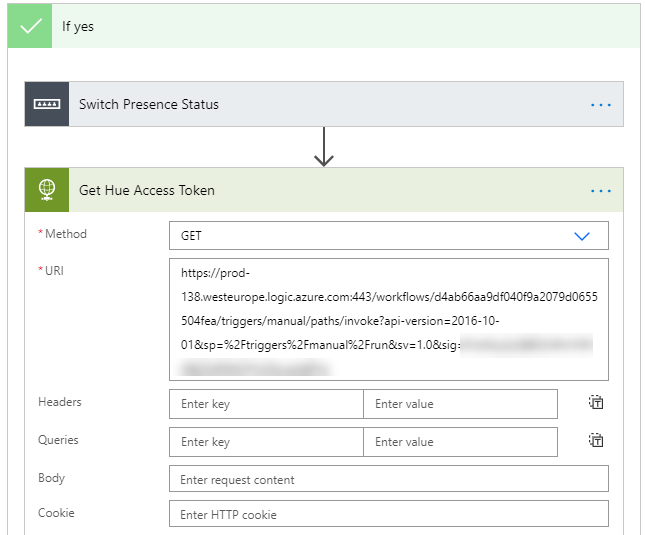
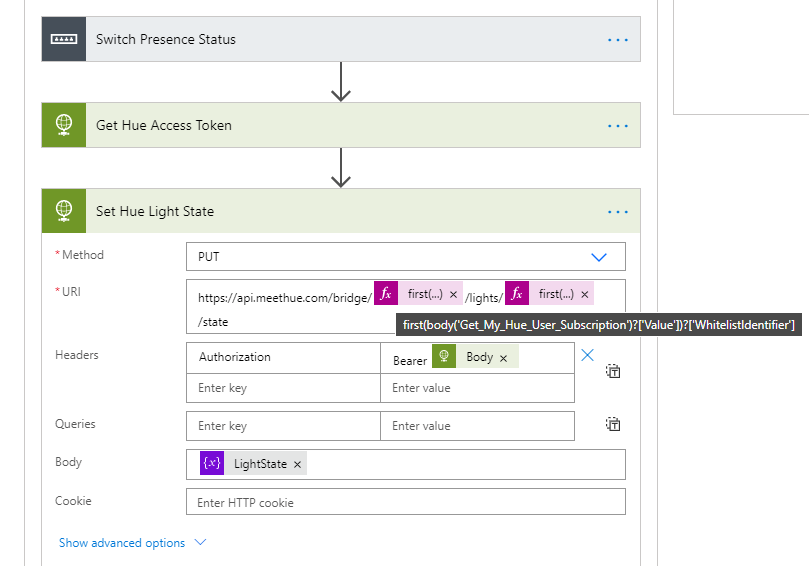
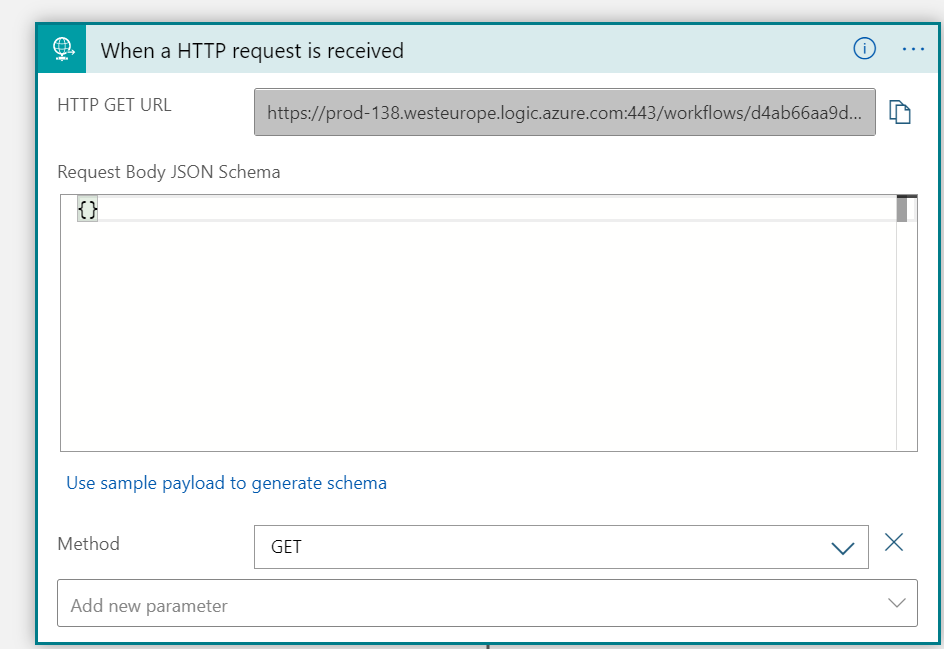
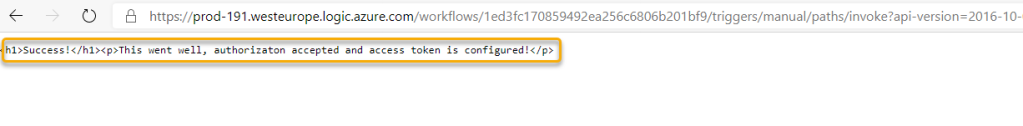
To trigger a Logic App using a HTTP trigger, you need to know the endpoint URL, for example:
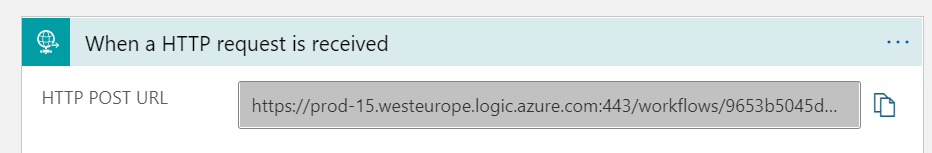
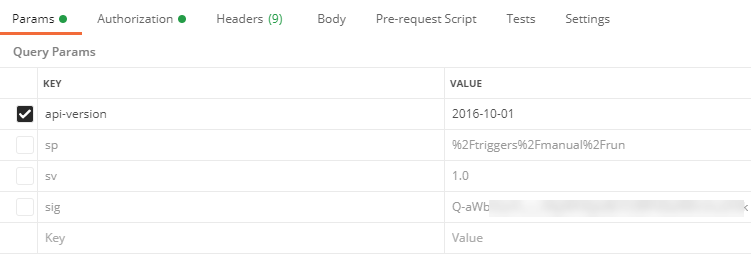
This URL consist of the endpoint address of the Logic App and workflow trigger, and with the following query parameters:
- api-version
- sp (specifies permissions for permitted HTTP methods to use)
- sv (SAS version to use)
- sig (shared access signature)
Anyone with access to this URL and query parameters kan trigger the Logic App, so it’s very important to protect it from unauthorized access and use.
In this multi part blog post series we will look into how Logic Apps can be protected by Azure AD.
Scenarios this multi-part blog post articles will cover:
- Provide Management Access Tokens and Restrict Issuer and Audience via OAuth
- Restrict External Guest User Access
- Expose Logic App as API
- Restrict permitted Enterprise Application Users and Groups and Conditional Access policies.
- Scopes and Roles Authorization in Logic Apps.
- Logic Apps and APIM (Azure API Management).
Lets first look at the other methods for protecting Logic Apps you should be aware of.
Protect Logic Apps Keys and URLs
Before we move on to protecting Logic Apps with Azure AD Open Authentication (OAuth), lets take a quick summary of other protections you should be aware of:
- Regenerate access keys. If you have reason to think SAS keys are shared outside your control, you can regenerate and thus making previous SAS keys invalid.
- Create expiring Callback URLs. If you need to share URLs with people outside your organization or team, you can limit exposure by creating a Callback URL that expire on a certain date and time.
- Create Callback URL with primary or secondary key. You can select to create the Callback URL with the specified primary or secondary SAS key.
The above methods should be part of any governance and security strategy for protecting Logic Apps that perform privilieged actions or might return sensitive data.
Protect Logic Apps via restricting inbound IP address
Another way to protect Logic Apps is to restrict from where the Logic App can be triggered via inbound IP address restrictions.
This opens up scenarios where you can specify your datacenter IP ranges, or only let other Logic Apps outbound IP addresses call nested Logic Apps, or only allow Azure API management to call Logic App.
Protect Logic Apps with Azure AD OAuth
By creating an Authtorization Policy for your Logic App you can use a Authorization header with a Bearer Token and require that the token contains the specified issuer, audience or other claims. Showing how that works in detail, and usable scenarios will be the main focus for this blog post.
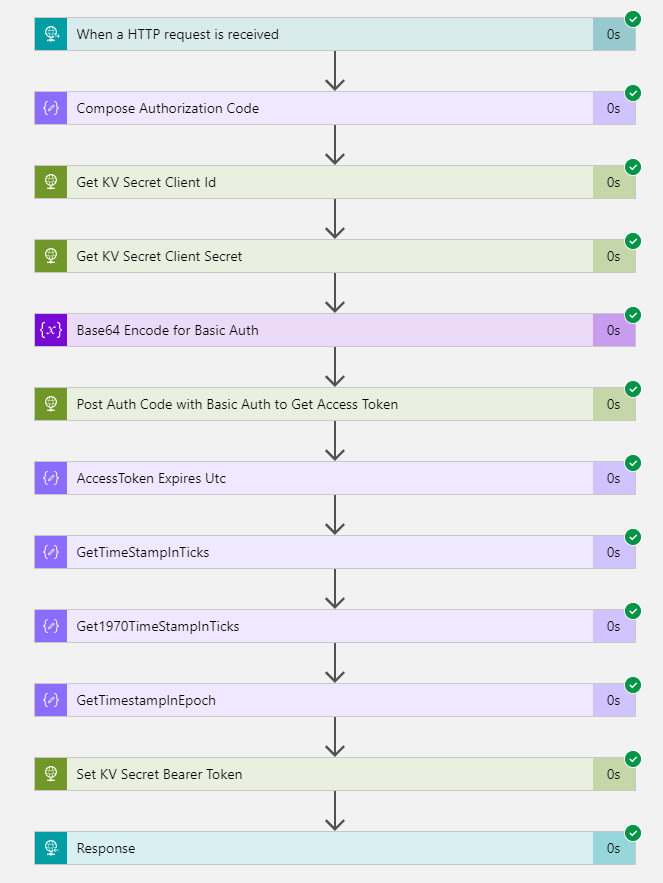
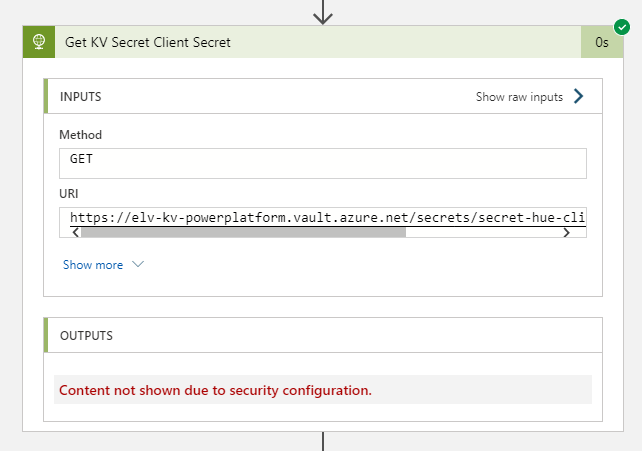
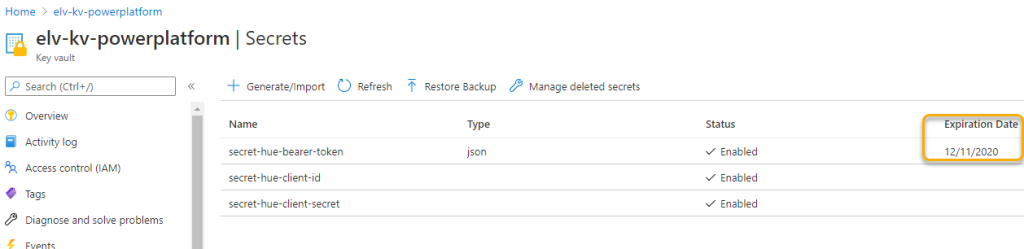
Let’s start by building a basic Logic App we can use for demo purpose.
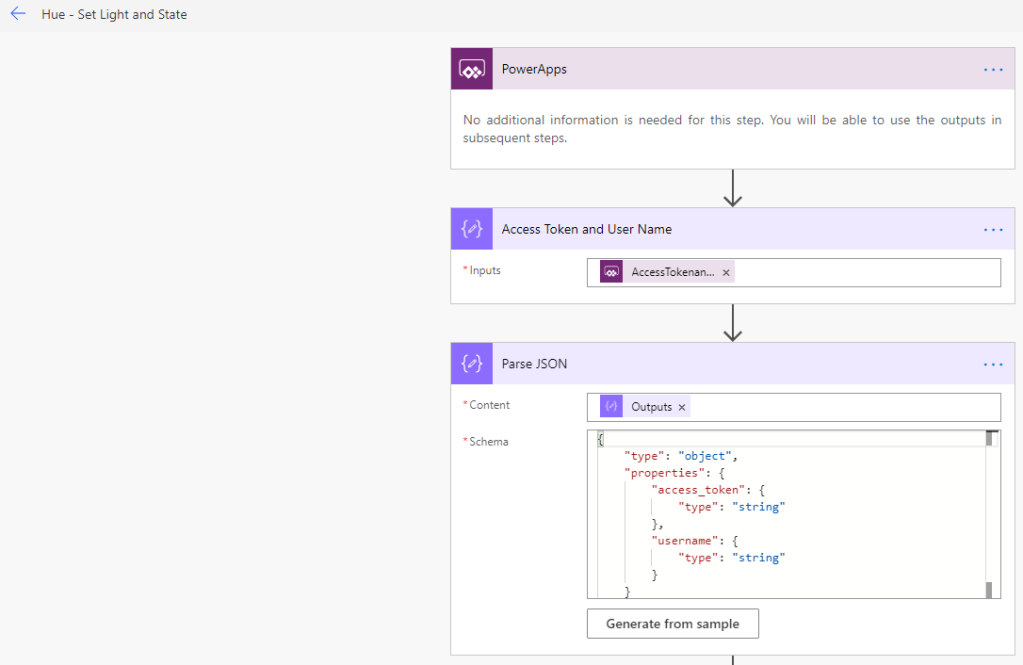
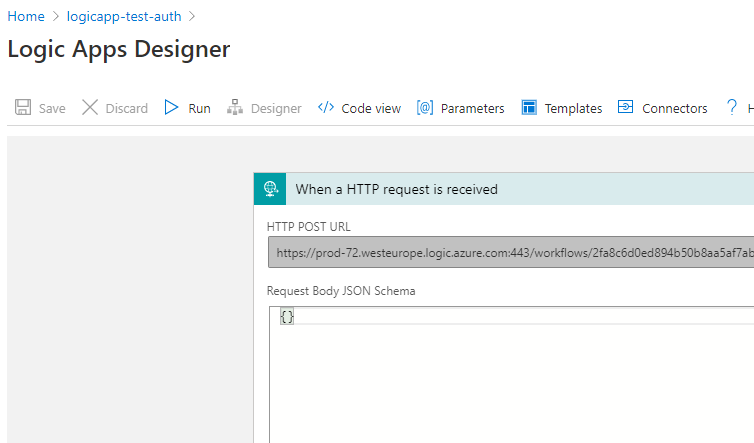
Creating a basic Logic App with HTTP Trigger and Response
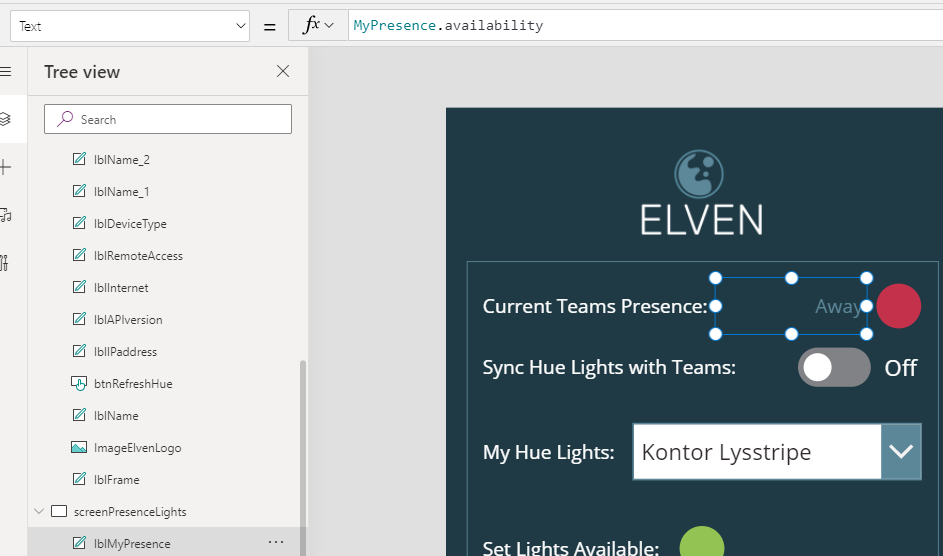
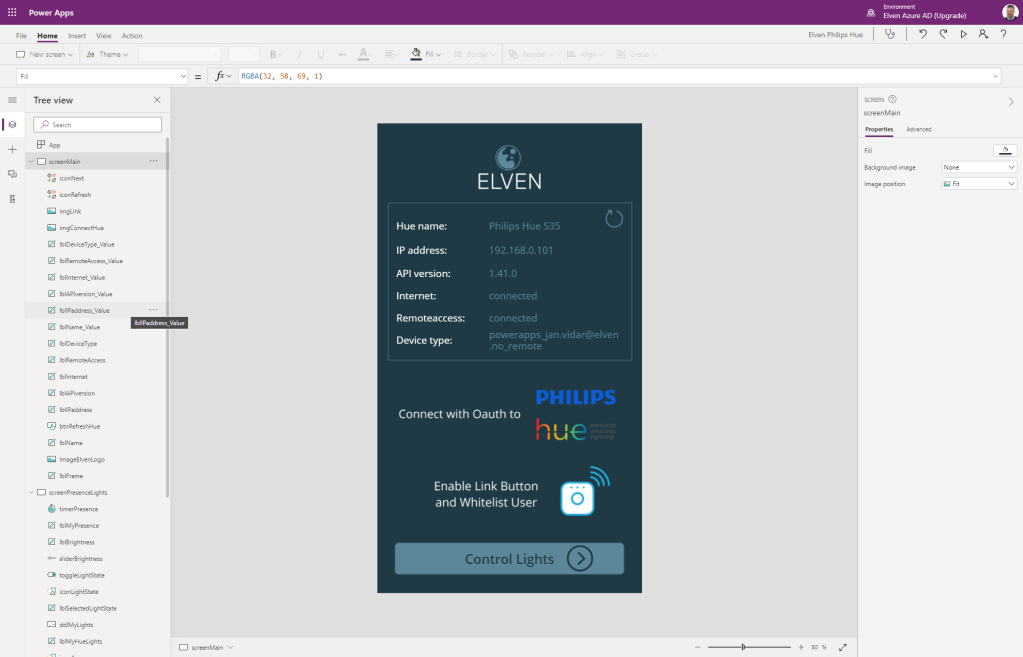
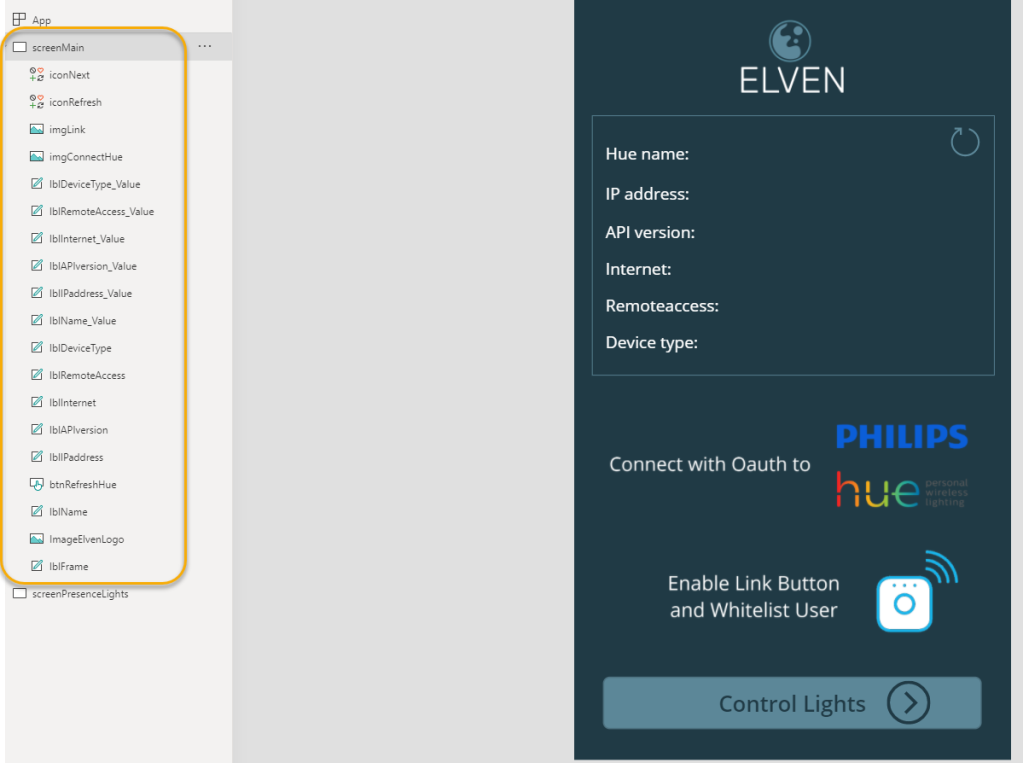
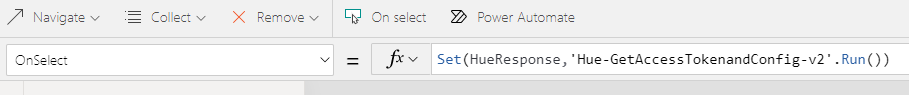
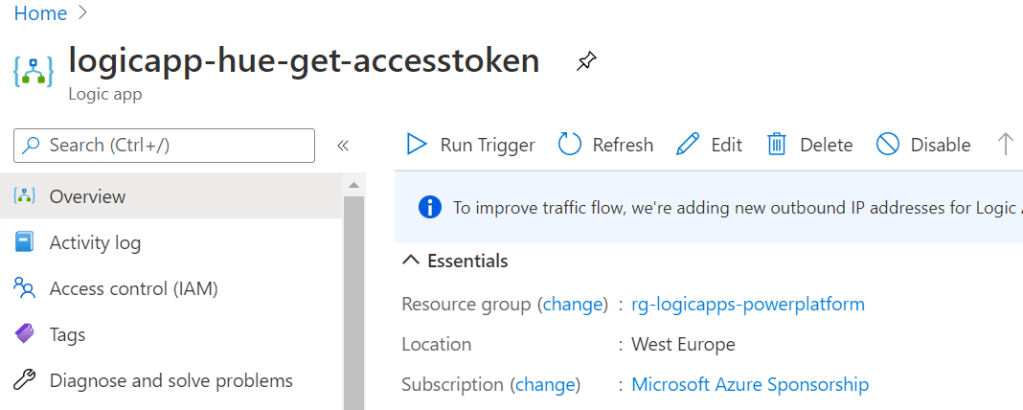
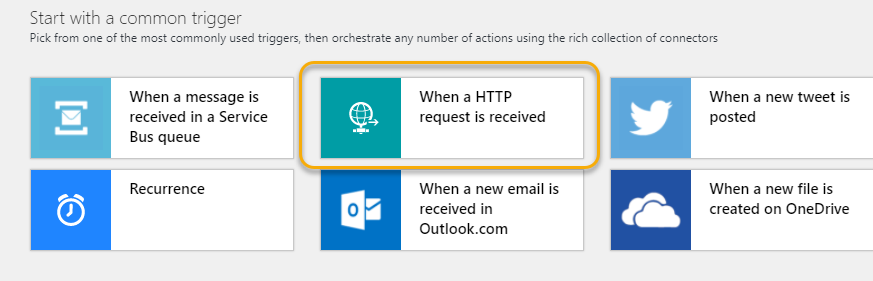
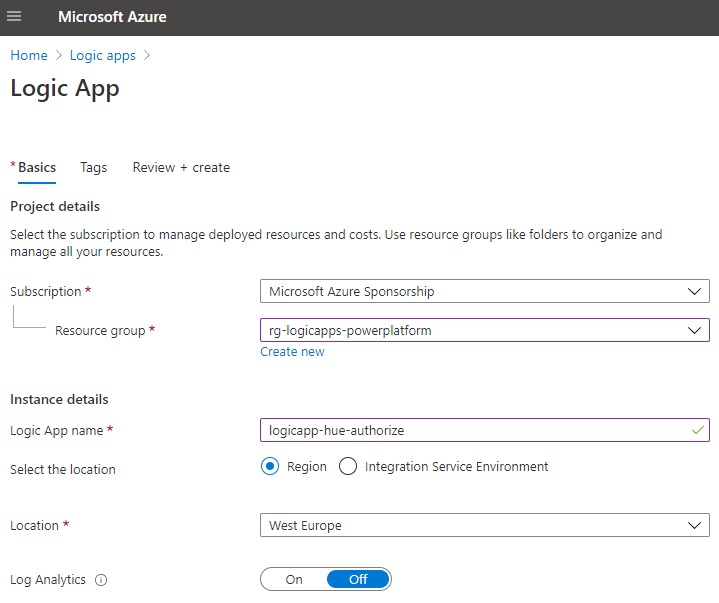
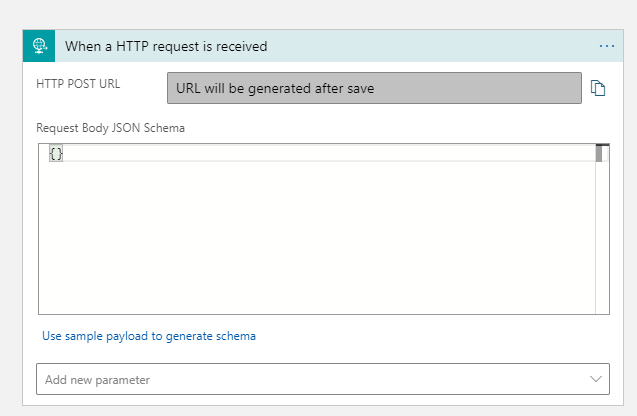
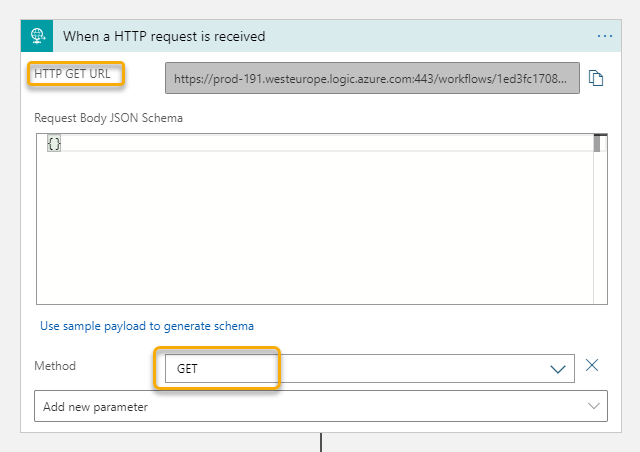
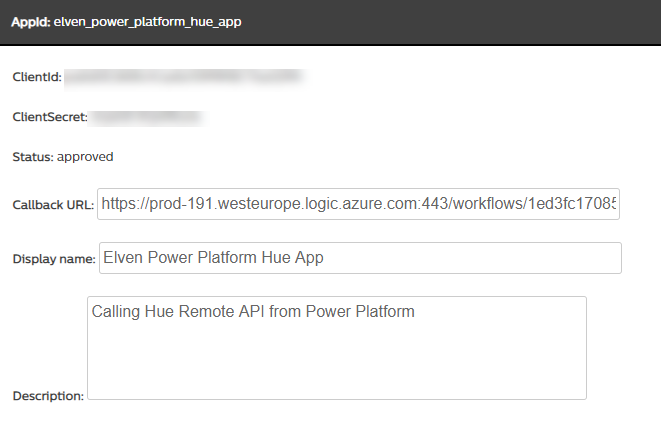
In you Azure Subcription, create a new Logic App, specifying to use a HTTP trigger. In my example below I have named my Logic App “logicapp-test-auth”:
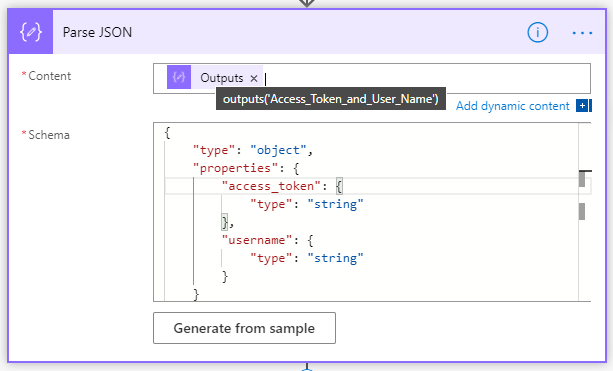
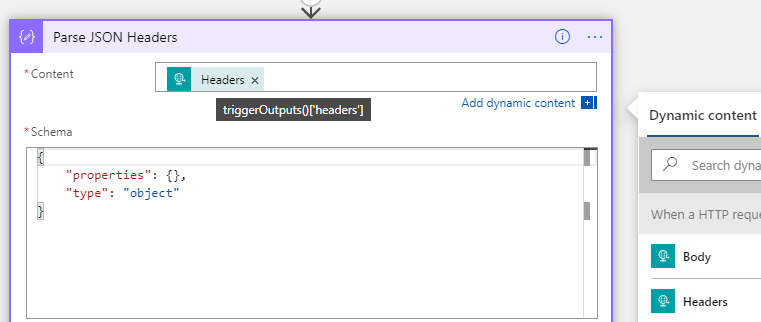
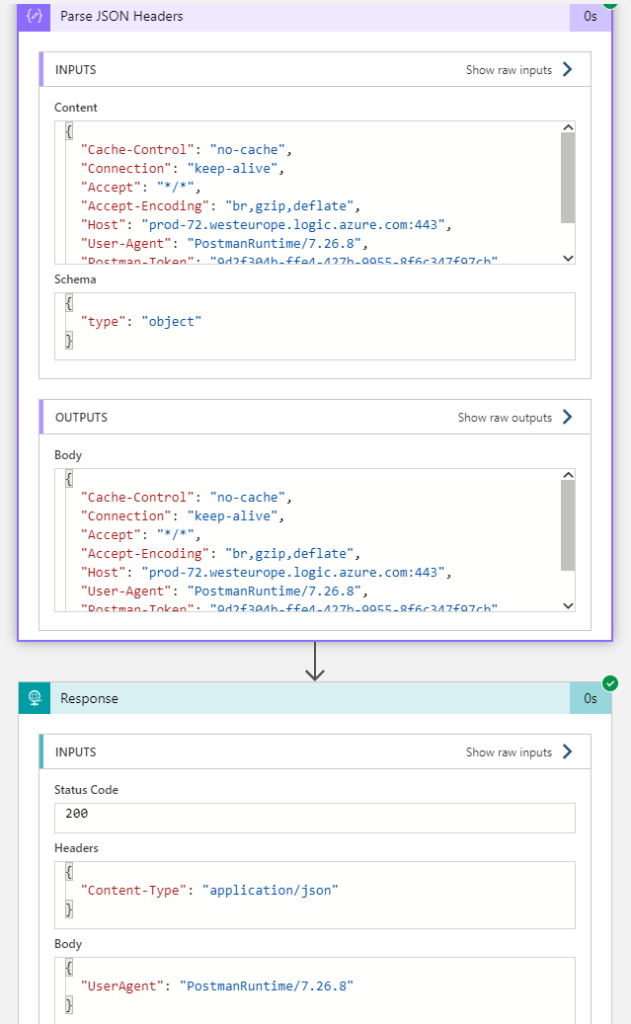
Next, add a Parse JSON action, where the Content is set to the trigger headers, as shown below. I’ve just specified a simple schema output, this can be customized later if needed:
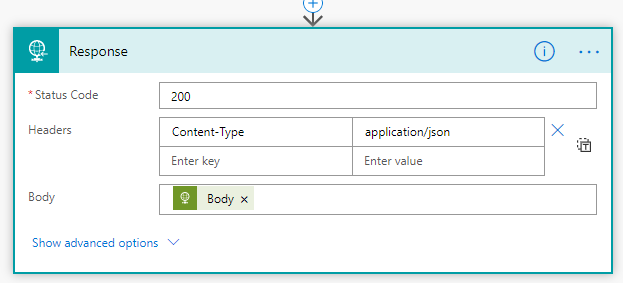
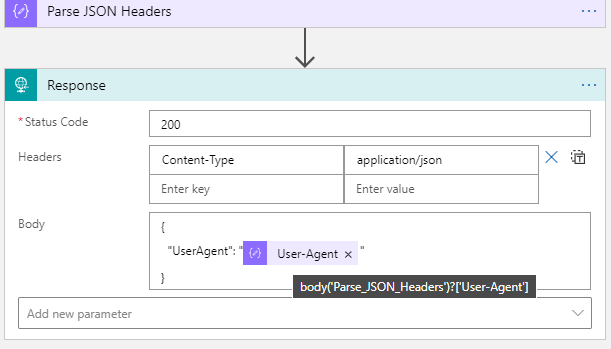
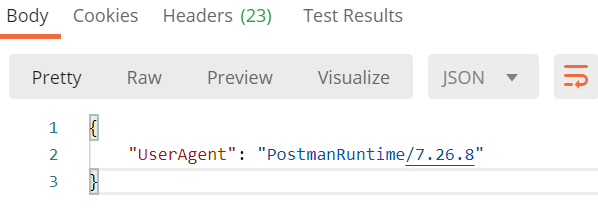
After that activity, add a Response action to return data to the caller. In my example below I return a Status Code of 200 (OK), and set the Content-Type to application/json, and return a simple JSON body of UserAgent where the value is set to the parsed header output from the trigger, using dynamic expression: body('Parse_JSON_Headers')?['User-Agent']
Testing Logic App with Postman
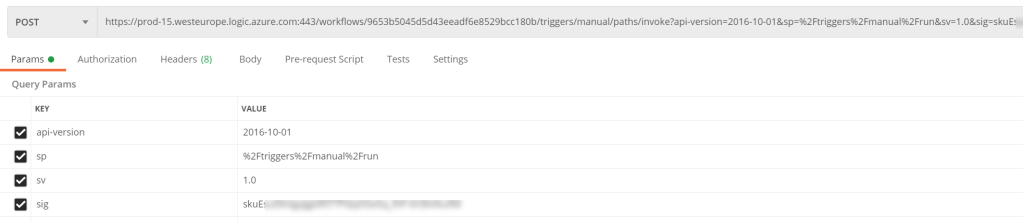
A great way to test and explore HTTP and REST API calls from your client is to use Postman (Download Postman | Try Postman for Free). When testing the above Logic App, paste in the HTTP POST URL for your trigger, and set the method to POST as shown below:
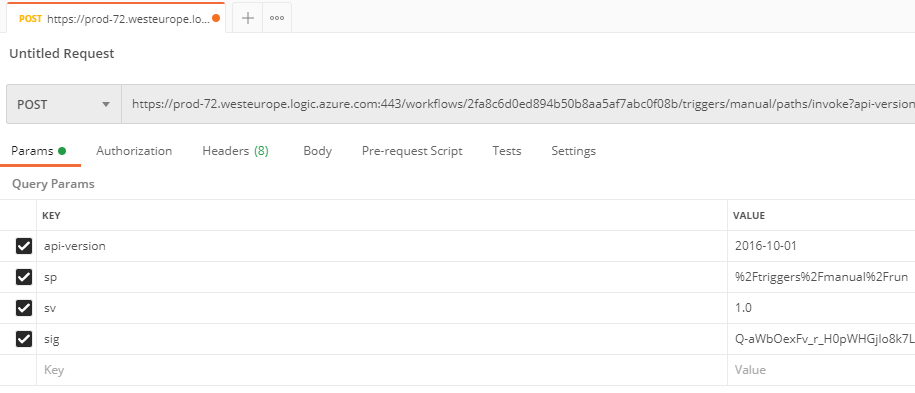
From the above image, you can see the URL, and also the query parameters listed (api-version, sp, sv, and sig, remember that these should be shared publicly).
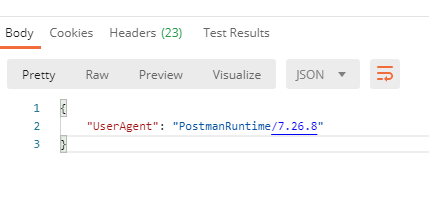
When I send the request, it will trigger the Logic App, and should response back:
We can also verify the run history for the Logic App:
We have now successfully tested the Logic App using SAS authentication scheme, and can proceed to adding Azure AD OAuth. First we need to create an Authorization Policy.
Creating an Azure AD Authorization Policy
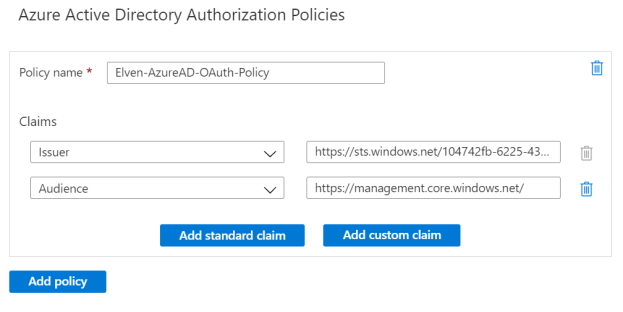
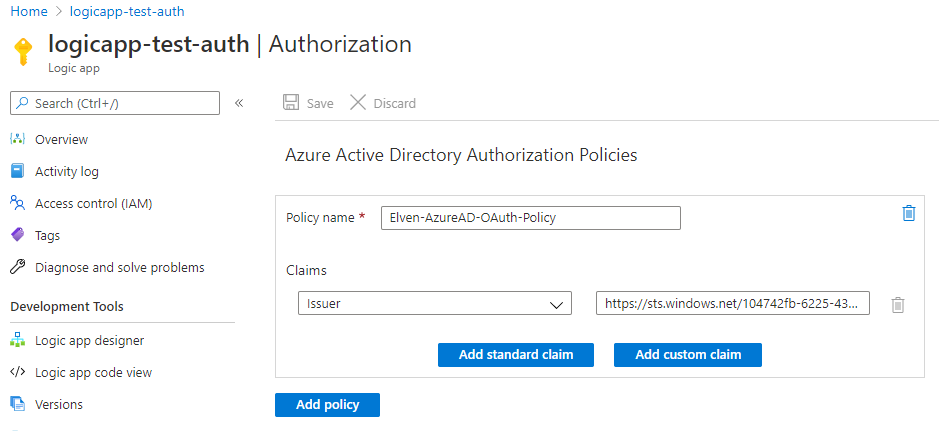
Under Settings and Authorization for your Logic App, add a new Authorization Policy with your name, and add the Issuer claim for your tenant. Issuer will be either https://sts.windows.net/{your-tenant-id}/ or https://login.microsoftonline.com/{your-tenant-id}/ depending on the version of the Access Token:
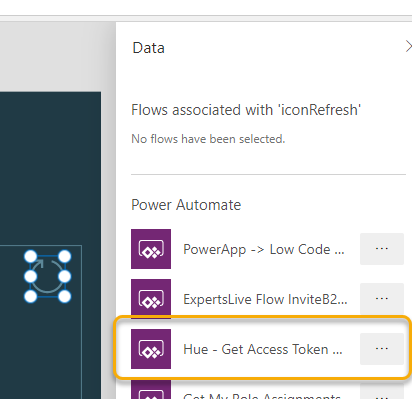
We will add more Claims later, but for now we will just test against the Issuer. Before we can test however, we need to get an Access Token. There are several ways to easily get an access token, basically we can consider one of the following two scenarios:
- Aquire an Access Token for well known Azure Management Resource Endpoints.
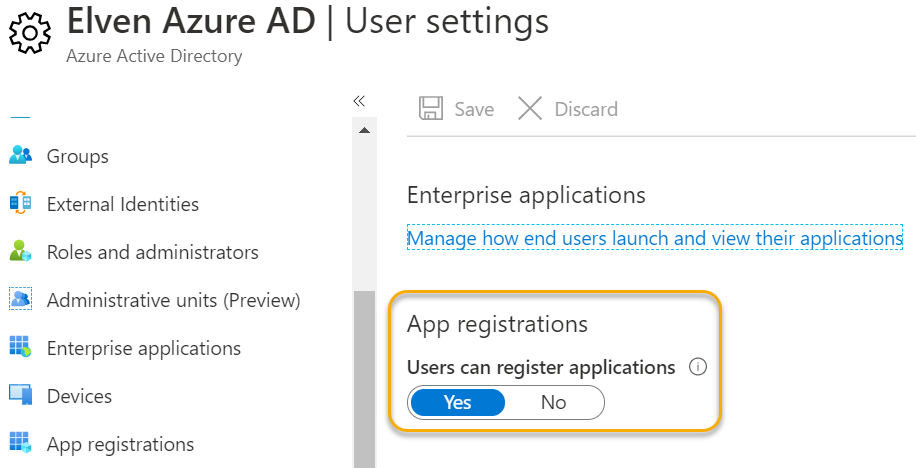
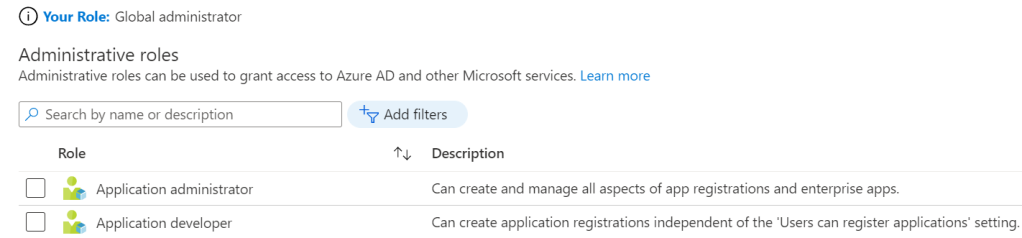
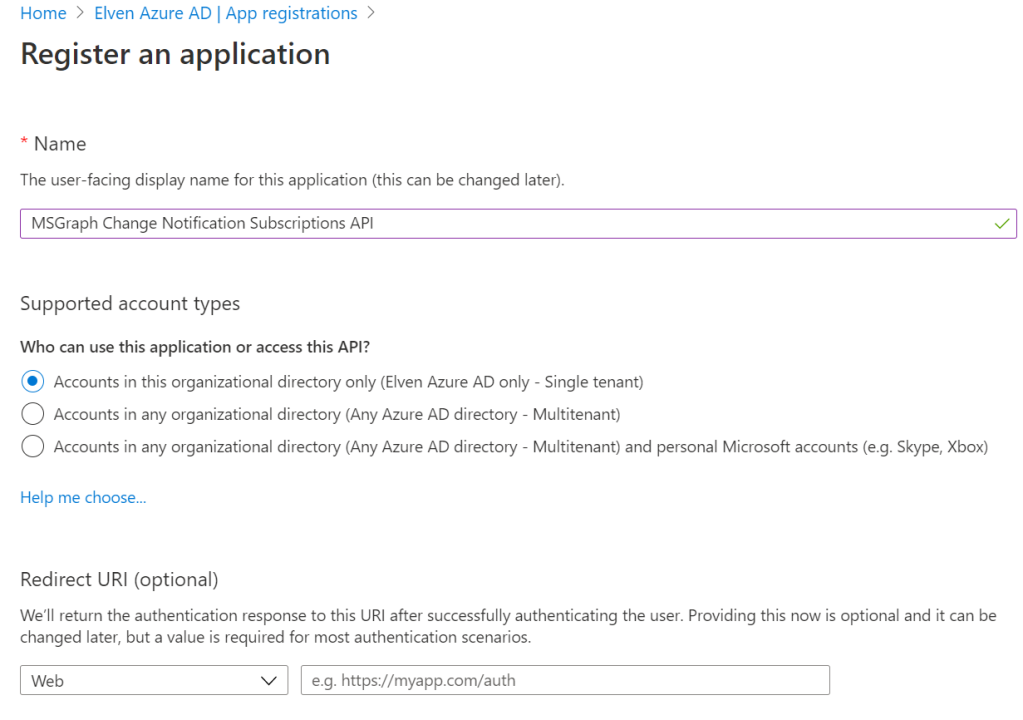
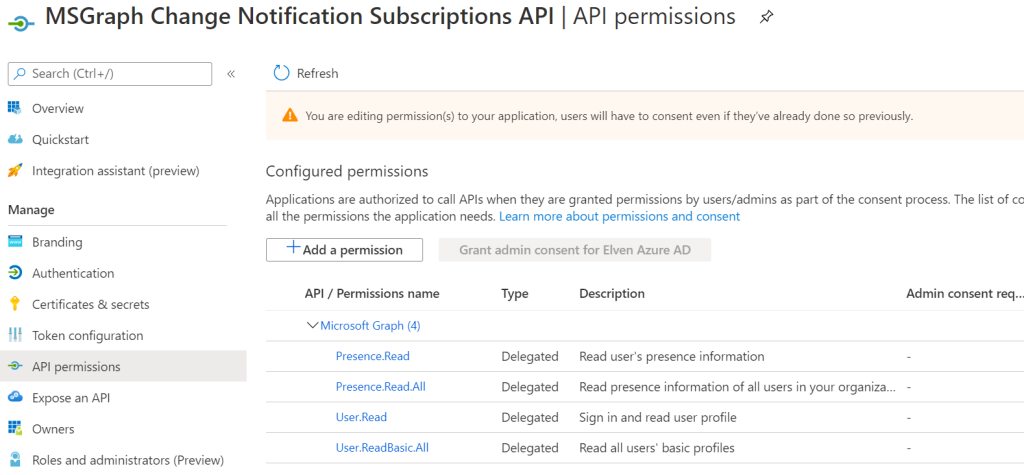
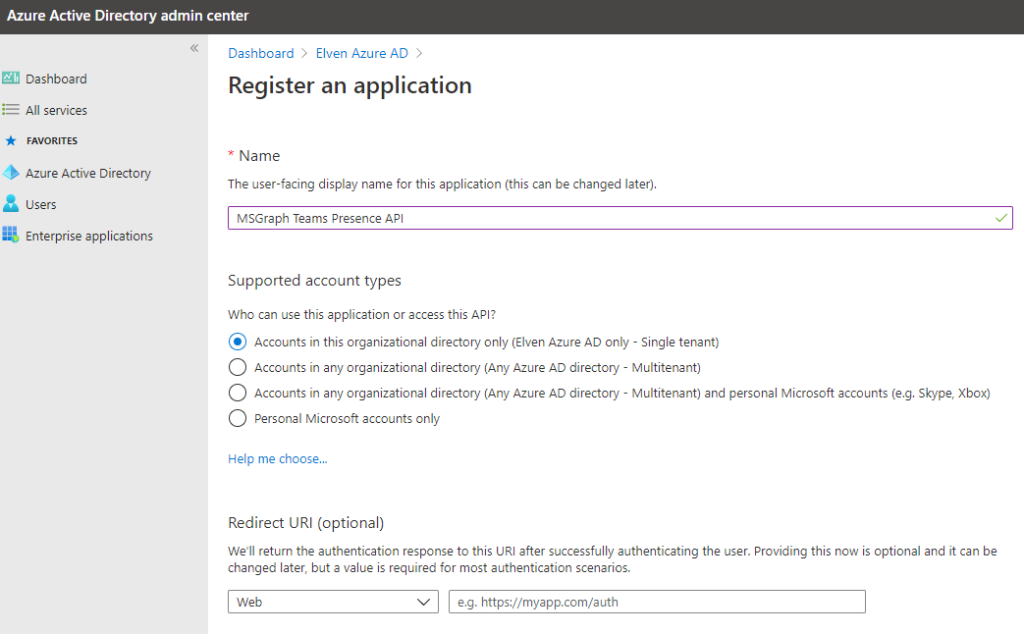
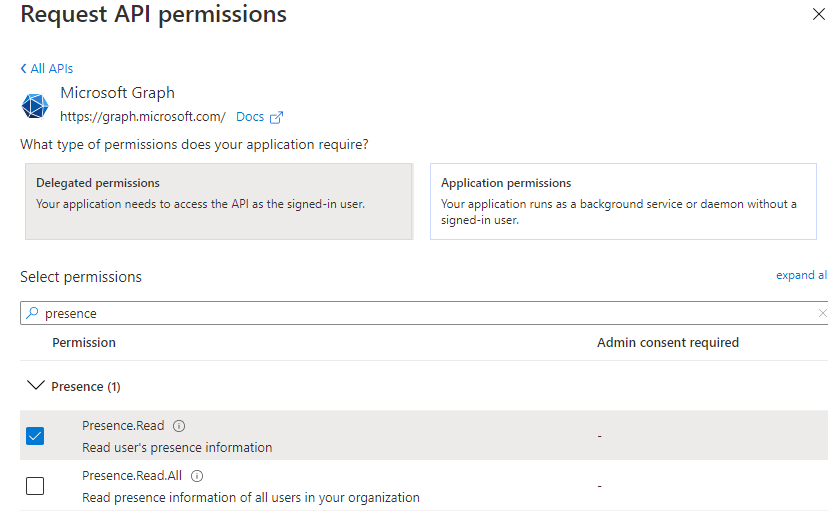
- Create an App Registration in Azure AD exposing an API.
We’ll cover App Registration and more advanced scenarios later, but for now we will get an Access Token using well known resource endpoints for Azure management.
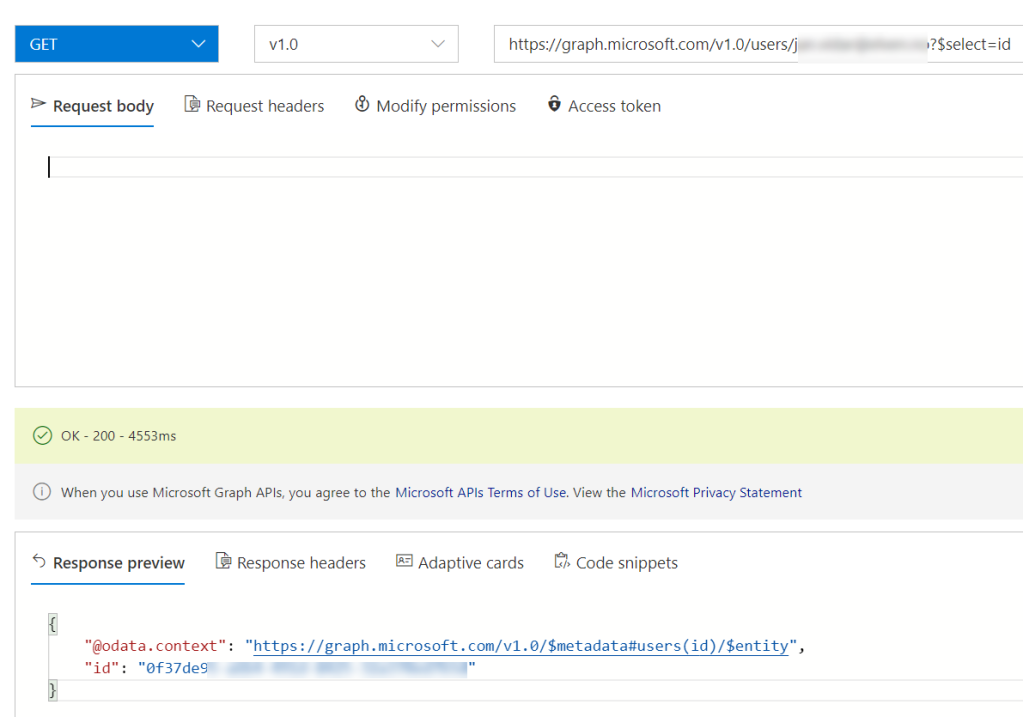
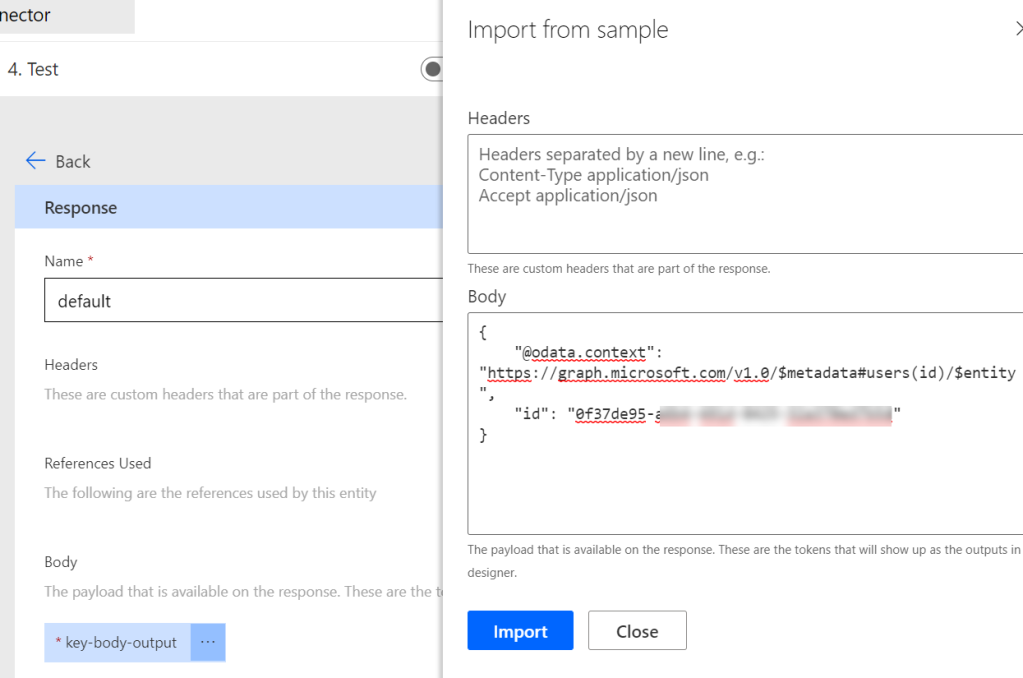
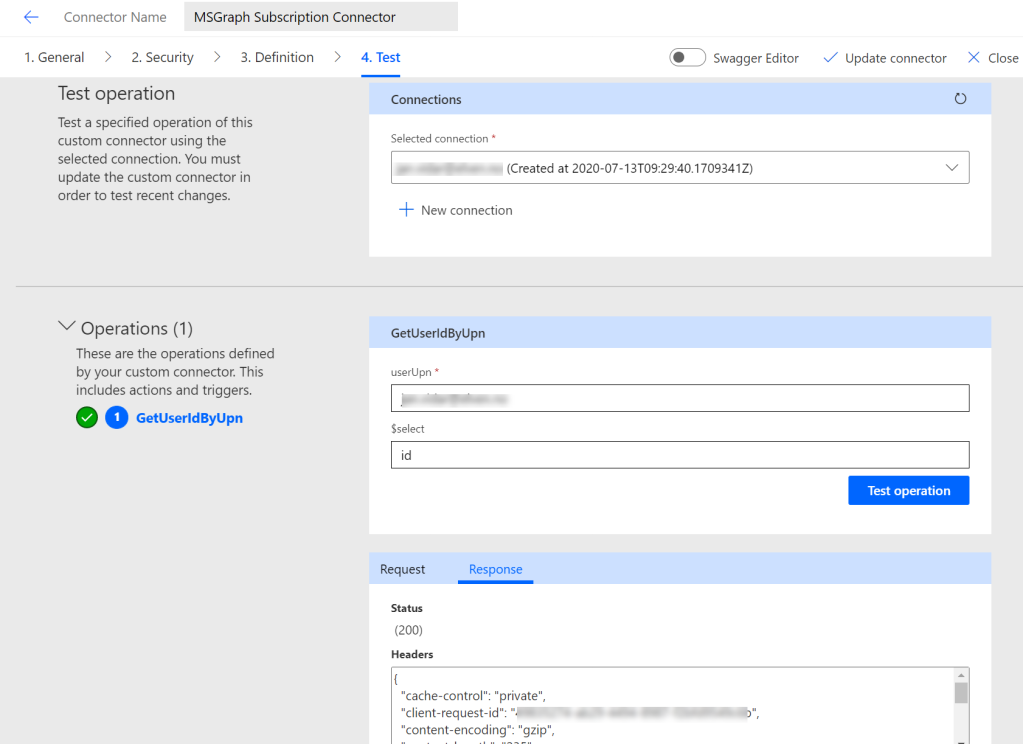
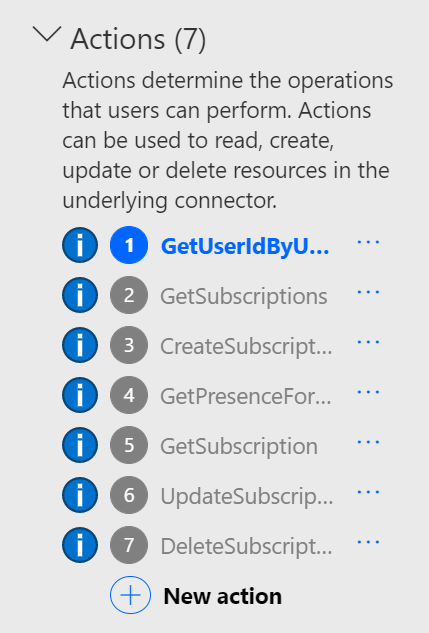
PS! Just a quick note on Access Tokens aquired for Microsoft Graph resources: These cannot be used for Logic Apps Azure AD OAuth authorization policies, because Graph access tokens does not allow for signature validation.
Management Access Tokens
The following examples require that you either have installed Azure CLI (Install the Azure CLI | Microsoft Docs) or Az PowerShell (Install Azure PowerShell with PowerShellGet | Microsoft Docs).
Azure CLI
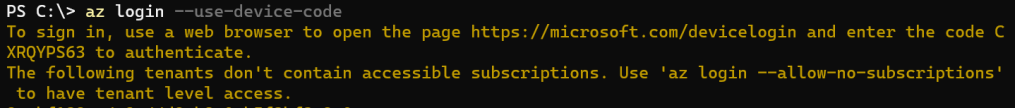
If you haven’t already, you will first need to login to Azure using az login. You can login interactively using default browser which supports modern authentication, including MFA, but if you are running multiple browsers and profiles it might be easier to use the device code flow:
az login --use-device-codeYou will be prompted to open the microsoft.com/devicelogin page and enter the supplied device code, and after authentication with your Azure AD account, you will get a list of all subscriptions you have access to.
PS! If your account has access to subscriptions in multiple tenants, you can also specify which tenant to log into using:
az login --tenant elven.onmicrosoft.com --use-device-codeTo get an Access Token you can just run az account get-access-token, like the following:
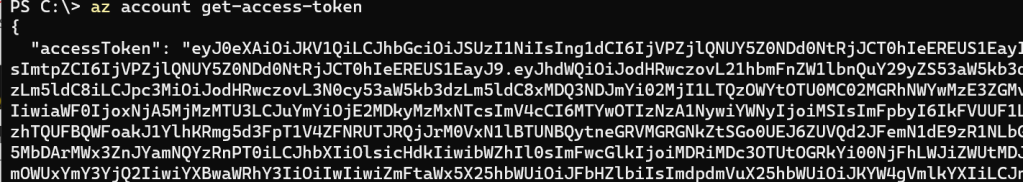
Let’s save that into a variable and get the token:
$accessToken = az account get-access-token | ConvertFrom-Json
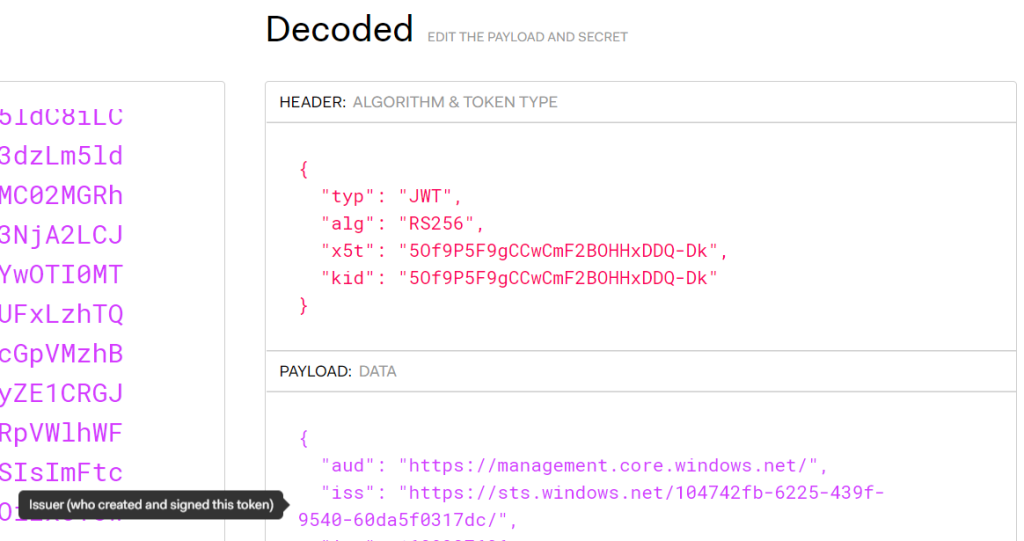
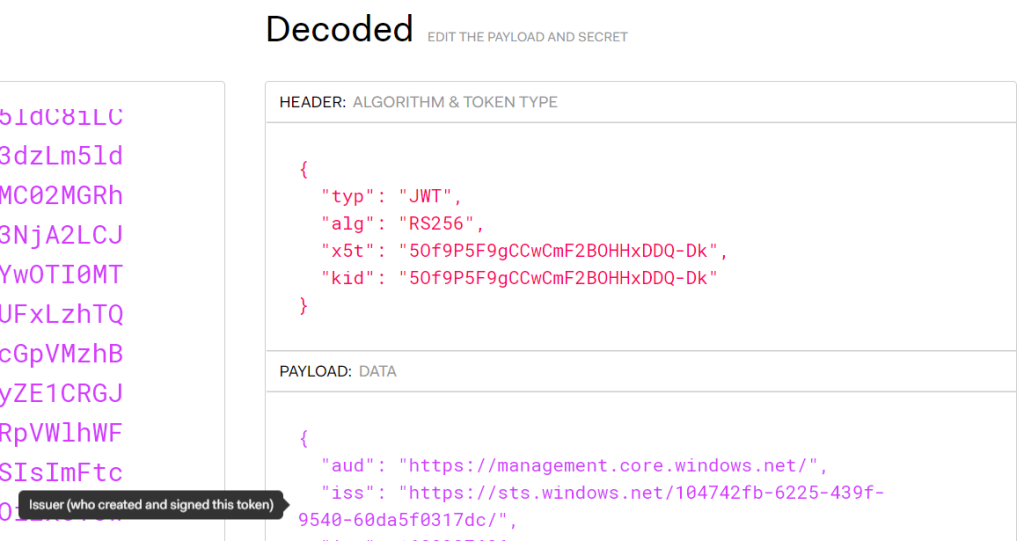
$accessToken.accessToken | ClipThe above command copies the Access Token to the Clipboard. Let’s take a look at the token. Open the website jwt.ms or jwt.io, and paste in the token. From the debugger you can look at the decoded token payload. The most interesting part for now is the issuer (iss) and audience (aud), which tells us where the token has been issued from, and to which audience:
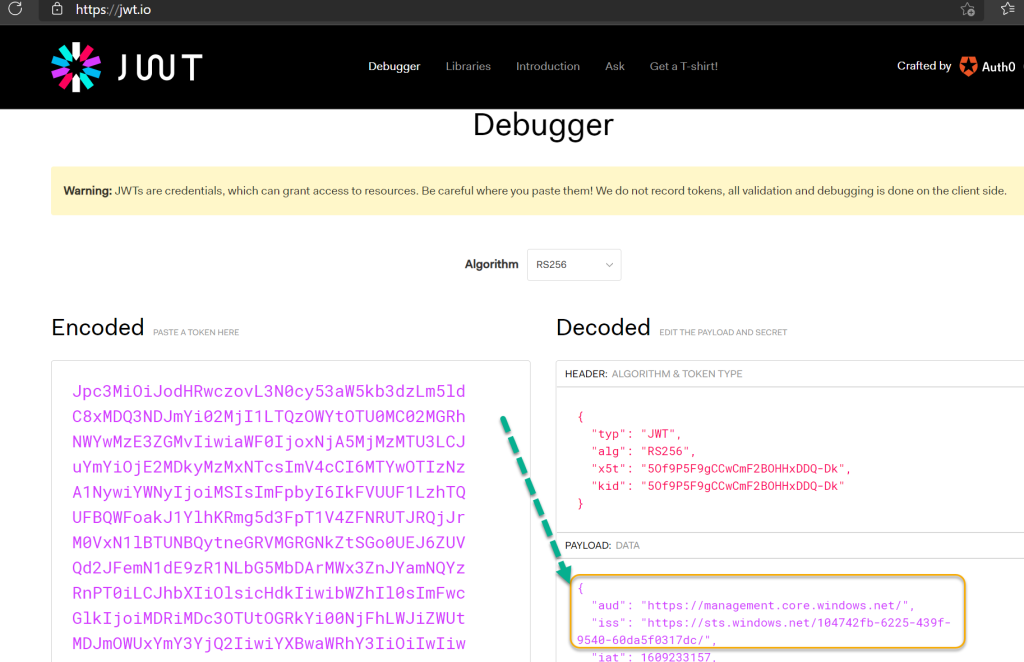
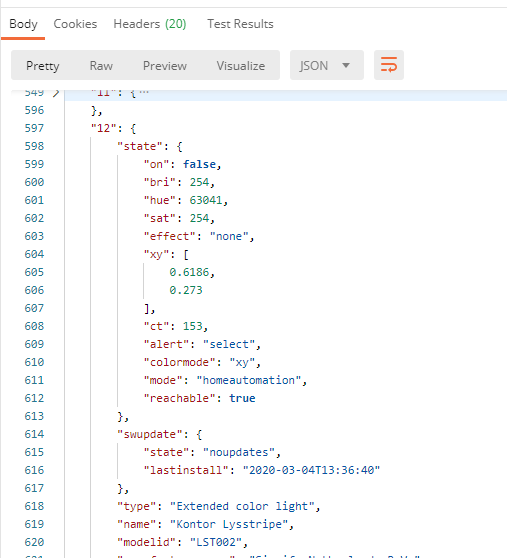
As we can see from above, the audience for the token is “management.core.windows.net”. You can also get an access token for a specific resource endpoint using:
$accessToken = az account get-access-token --resource-type arm | ConvertFrom-JsonTo show all available resource endpoints use:
az cloud show --query endpoints
Now that we have the method to get the access token using Az Cli, lets take a look at Az PowerShell as well. For reference for az account command and parameters, see docs here: az account | Microsoft Docs
Azure PowerShell
First you need to login to your Azure Subscription by using:
Connect-AzAccount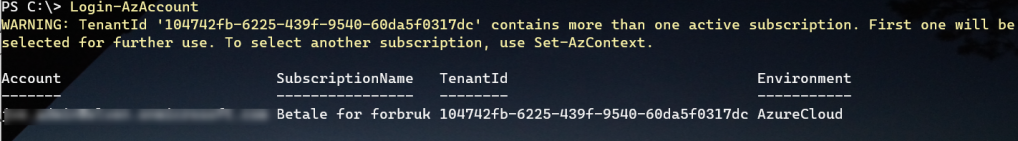
If your account has access to multiple subscriptions in multiple tenant, you can use the following command to specify tenant:
Connect-AzAccount -Tenant elven.onmicrosoft.comIf there are multiple subscriptions, you might need to specify which subscription to access using Set-AzContext -Subscription <Subscription>. Tip, use Get-AzContext -ListAvailable for listing available subscriptions.
To get an access token using Az PowerShell, use the following command to save to variable and copy to clipboard:
$accessToken = Get-AzAccessToken
$accessToken.Token | ClipWe can once again look at the JWT debugger to verify the token:
As with Az CLI, you can also specify resource endpoint by using the following command in Az PowerShell specifying the resource Url:
$accessToken = Get-AzAccessToken -ResourceUrl 'https://management.core.windows.net'
Now that we have the Access Token for an Azure Management resource endpoint, let’s see how we can use that against the Logic App.
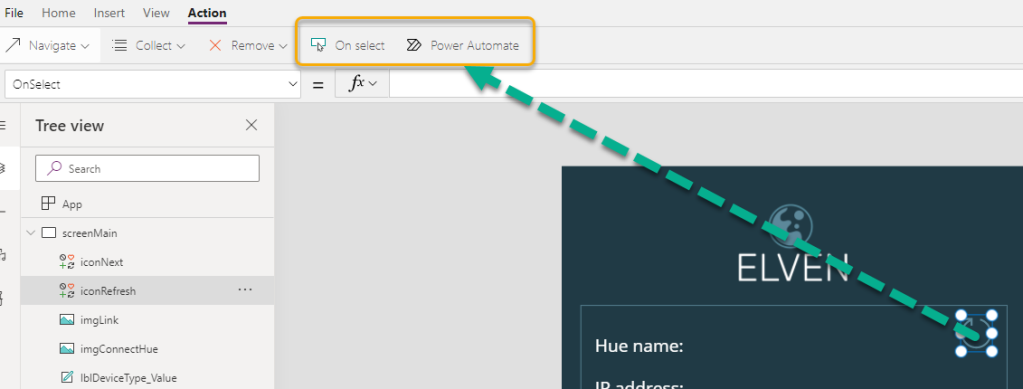
Use Bearer Token in Postman
From the previous test using Postman earlier in this article, go to the Authorization section, and specify Bearer Token, and then Paste the management access token you should still have in your clipboard like the following:
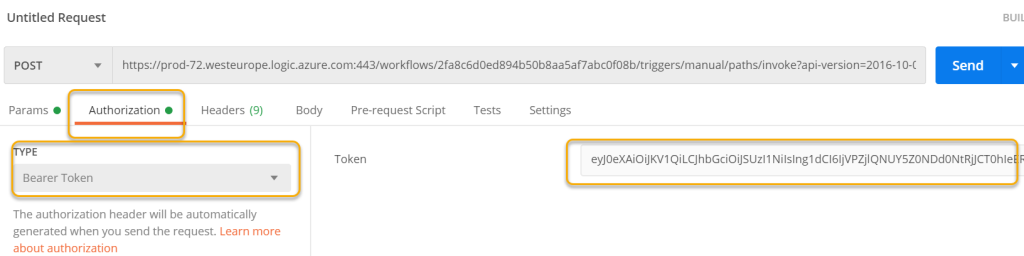
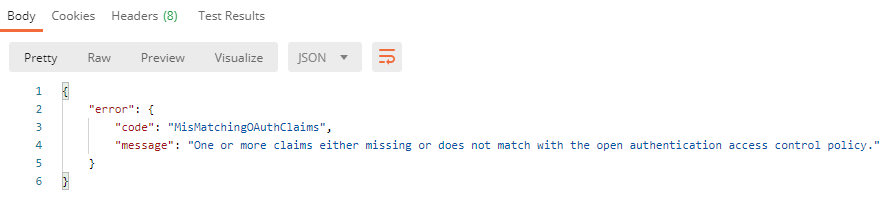
When clicking Send request, observe the following error:
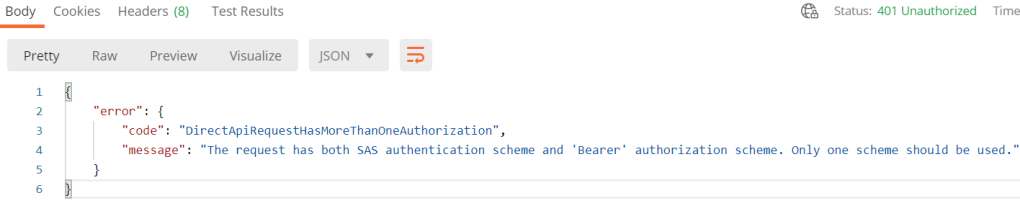
We cannot combine both SAS (Shared Access Signature) and Bearer Token, so we need to adjust the POST URL to the Logic Apps. In Postman, this can be easily done in Postman under Params. Deselect the sp, sv and sig query parameters like the following, which will remove these from the POST URL:
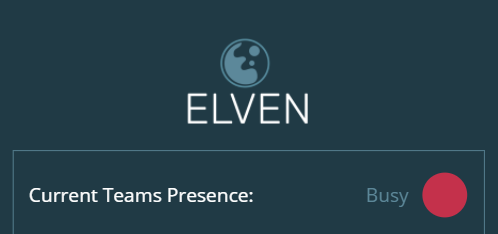
When you now click Send request, you should get a successful response again, provided that tha access token is valid:
Perfect! We have now authorized triggering the Logic App using Azure AD OAuth, based on the Authorization policy:
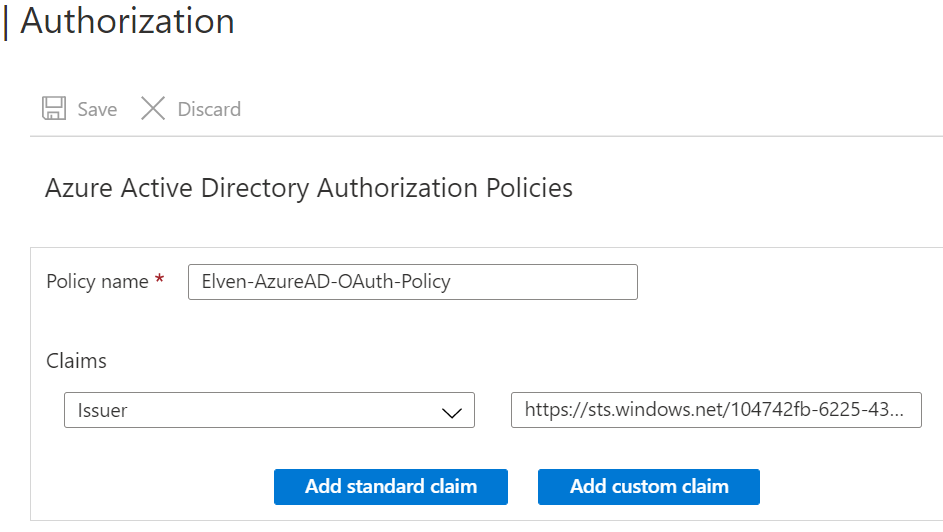
And the Access Token that match that Issuer:
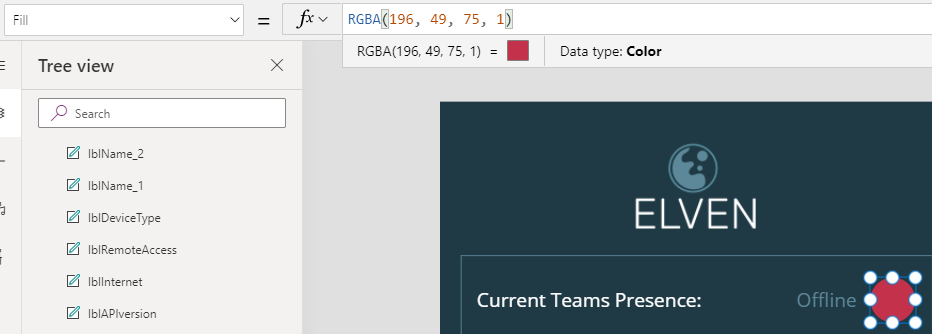
I will now add the audience to the Authorization Policy as well, so that only Access Tokens for the management endpoint resource can be used:
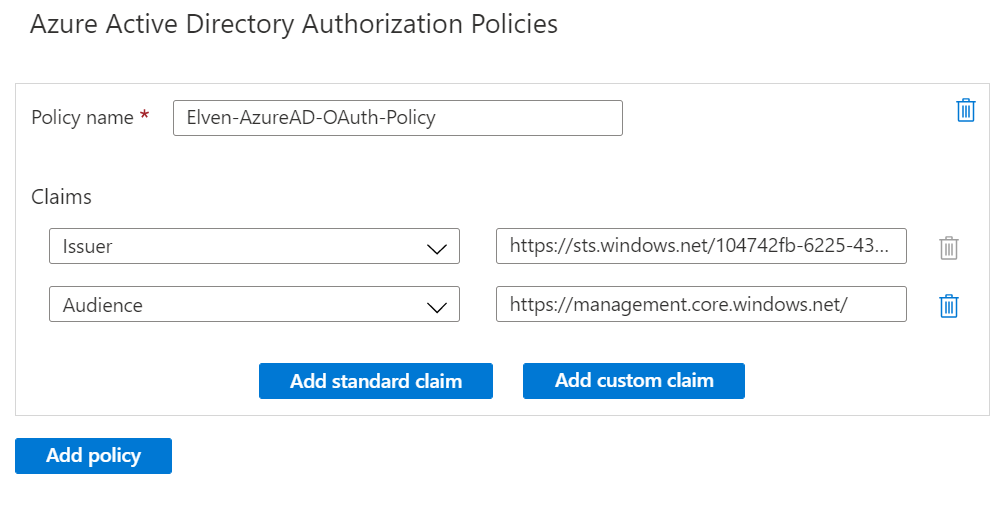
Any HTTP requests to the Logic App that has a Bearer Token that does not comply with the above Authorization Policy, will received this 403 – Forbidden error:
Test using Bearer Token in Azure CLI
You can trigger HTTP REST methods in Azure CLI using az rest --method .. --url ...
When using az rest an authorization header with bearer token will be automatically added, trying to use the url as resource endpoint (if url is one of the well known resource endpoints). As we will be triggering the Logic App endpoint as url, we need to specify the resource endpoint as well. In my example, I will run the following command for my Logic App:
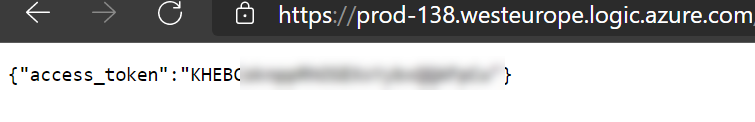
az rest --method POST --resource 'https://management.core.windows.net/' --url 'https://prod-72.we
steurope.logic.azure.com:443/workflows/2fa8c6d0ed894b50b8aa5af7abc0f08b/triggers/manual/paths/invoke?api-
version=2016-10-01'From above, I specify the resource endpoint of management.core.windows.net, from which the access token will be aquired for, and for url I specify my Logic App endpoint url, without the sp, sv and sig query parameters. This results in the following response:
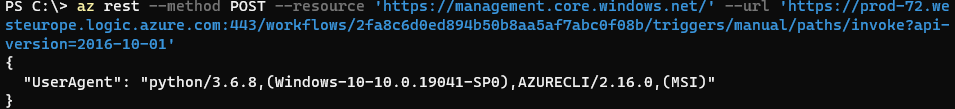
So the Logic App triggered successfully, this time returning my console (Windows Terminal using Azure CLI).
Test using Bearer Token in Azure PowerShell
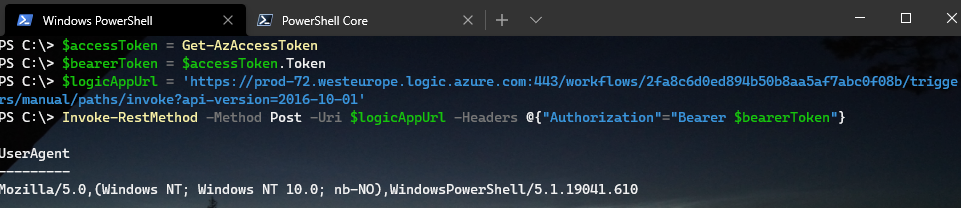
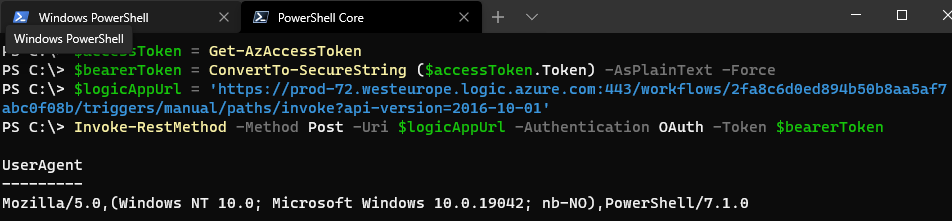
I will also show you how you can do a test using Az PowerShell. Make sure that you get an access token and saving the bearer token to a variable using this command first:
$accessToken = Get-AzAccessToken
$bearerToken = $accessToken.TokenI will also set the Logic App url to a variable for easier access:
$logicAppUrl = 'https://prod-72.westeurope.logic.azure.com:443/workflows/2fa8c6d0ed894b50b8aa5af7abc0f08b/triggers/manual/paths/invoke?api-version=2016-10-01'There are 2 ways you can use Az PowerShell, either using Windows PowerShell or PowerShell Core.
For Windows PowerShell, use Invoke-RestMethod and add a Headers parameter specifying the Authorization header to use Bearer token:
Invoke-RestMethod -Method Post -Uri $logicAppUrl -Headers @{"Authorization"="Bearer $bearerToken"}Running this should return this successfully, specifying my Windows PowerShell version (5.1) as User Agent:
For PowerShell Core, Invoke-RestMethod has now support for using OAuth as authentication, but I first need to convert the Bearer Token to a Secure String:
$accessToken = Get-AzAccessToken
$bearerToken = ConvertTo-SecureString ($accessToken.Token) -AsPlainText -Force
Then I can call the Logic App url using:
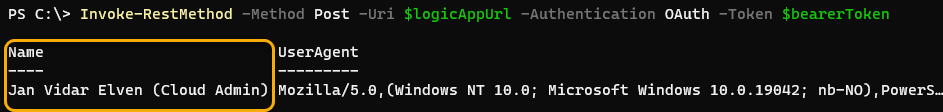
Invoke-RestMethod -Method Post -Uri $logicAppUrl -Authentication OAuth -Token $bearerToken
This should successfully return the following response, this time the User Agent is my PowerShell Core version (7.1):
Summary so far of Management Access Tokens and Logic Apps
At this point we can summarize the following:
- You can trigger your Logic App either by using SAS URL or using Bearer Token in Authorization Header, but not both at the same time.
- You can add an Azure AD Authorization Policy to your Logic App that specifies the Issuer and Audience, so that calling clients only can use Bearer Tokens from the specified issuer (tenant id), and audience (resource endpoint).
- While you cannot disable use of SAS signatures altogether, you can keep them secret, and periodically rollover, and only share the Logic App url endpoint and trigger path with clients.
- This is especially great for automation scenarios where users can use CLI or Azure PowerShell and call your Logic Apps securely using OAuth and Access Tokens.
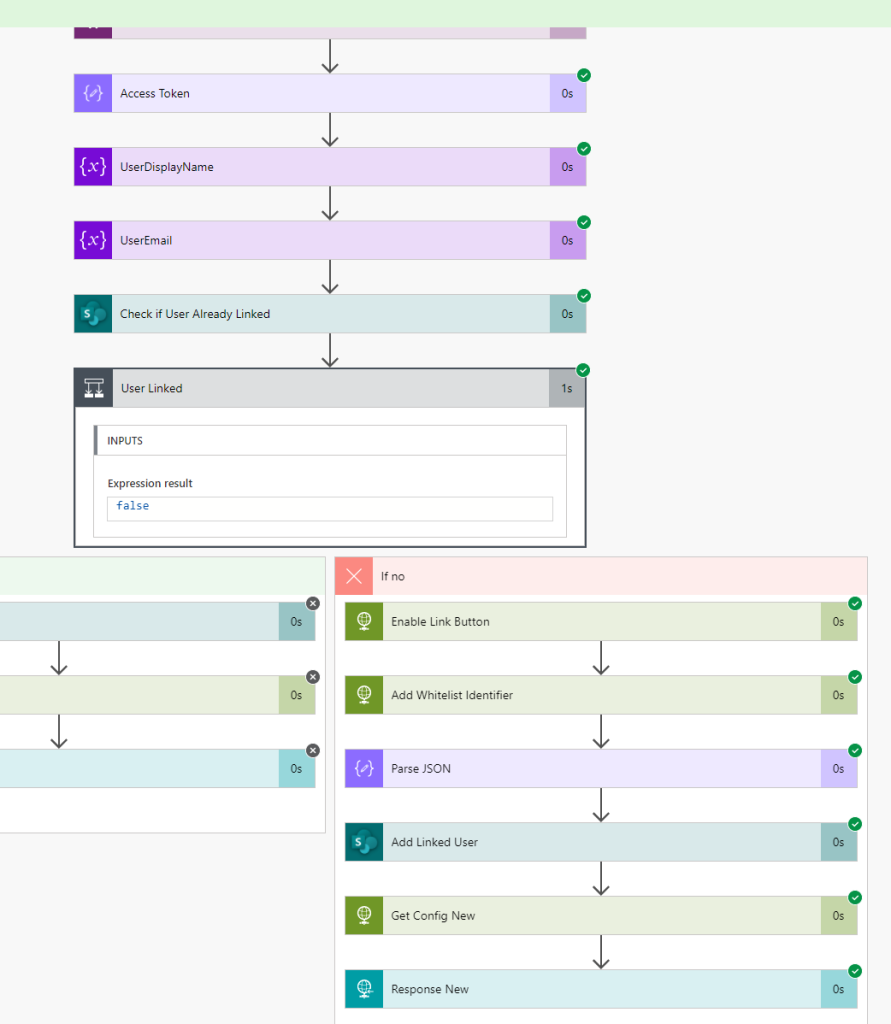
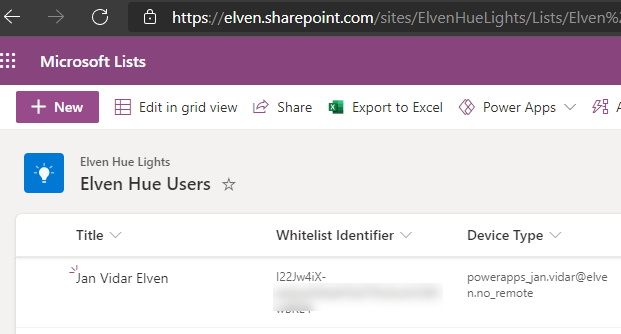
In the next part we will look more into how we can customize the Logic App to get the details of the Access Token so we can use that in the actions.
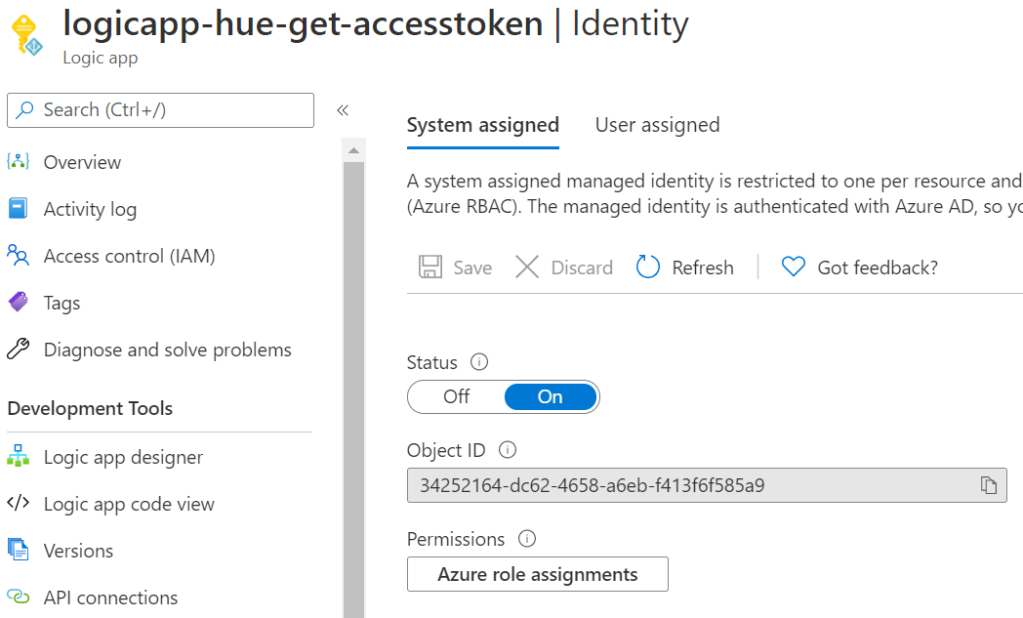
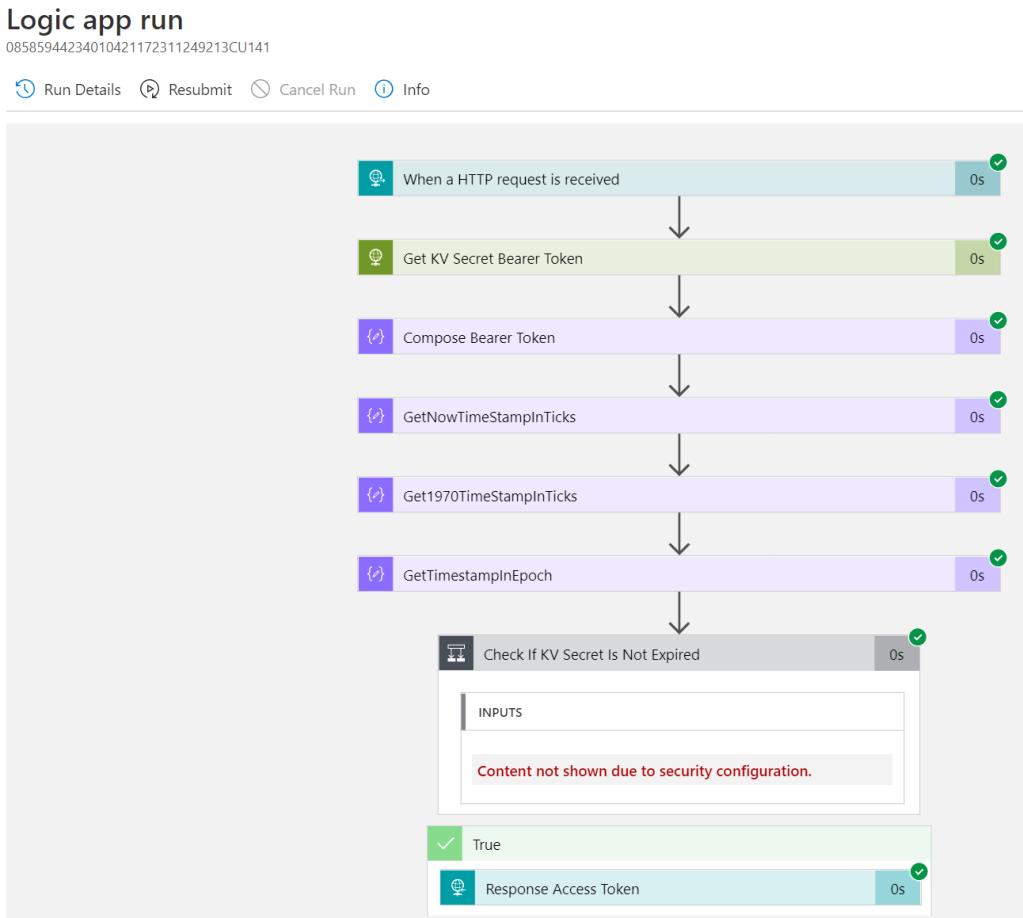
Include Authorization Header in Logic Apps
You can include the Authorization header from the OAuth access token in the Logic App. To do this, open the Logic App in code view, and add the operationOptions to IncludeAuthorizatioNHeadersInOutputs for the trigger like this:
"triggers": {
"manual": {
"inputs": {
"schema": {}
},
"kind": "Http",
"type": "Request",
"operationOptions": "IncludeAuthorizationHeadersInOutputs"
}
}For subsequent runs of the Logic App, we can now see that the Authorization Header has been included:
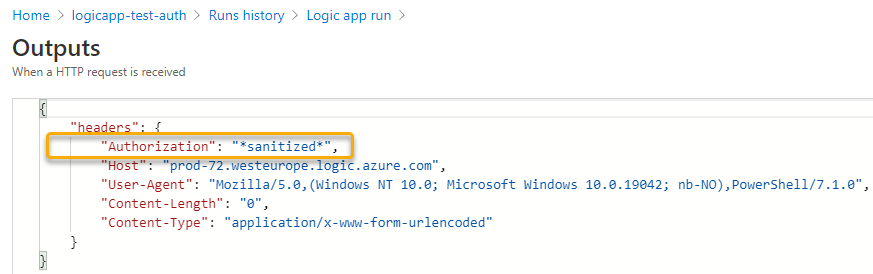
And if we parse the headers output, we can access the Bearer Token:
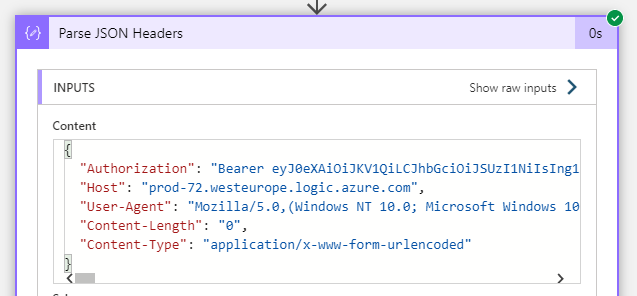
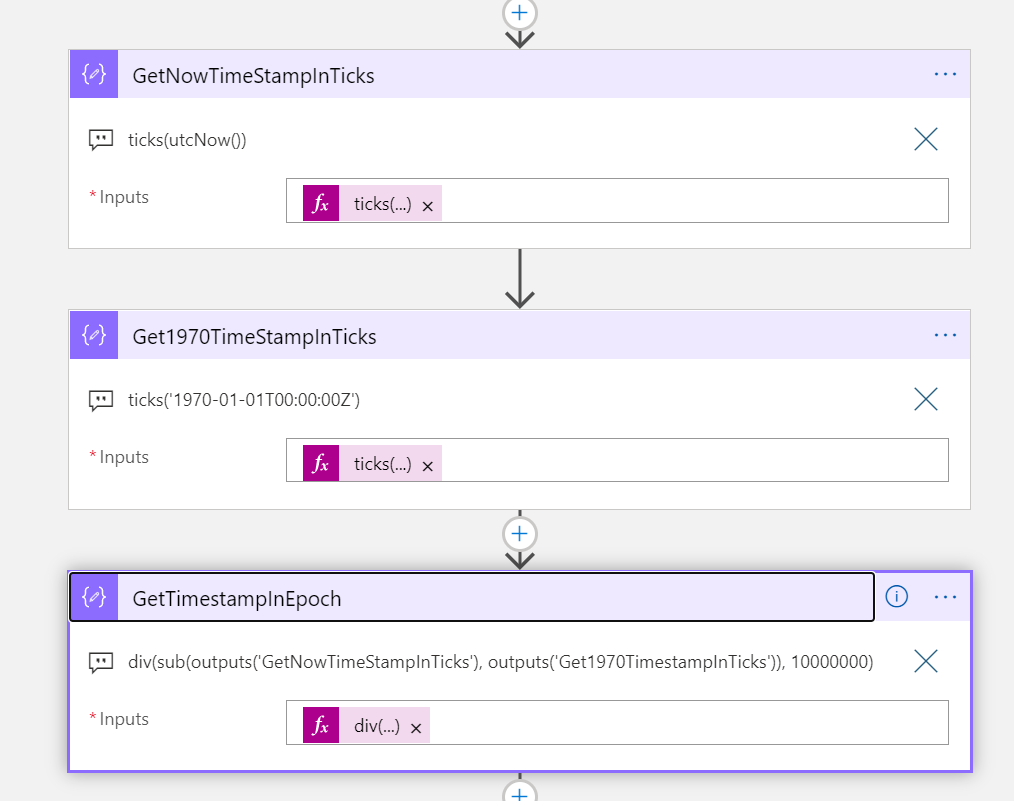
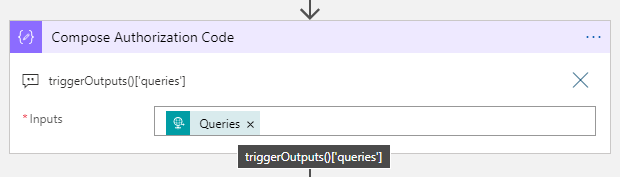
If we want to decode that Bearer token to get a look into the payload claims, we can achieve that with some custom expression magic. Add a Compose action to the Logic App and use the following custom expression:
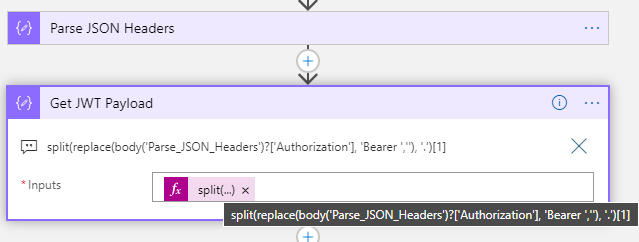
Let’s break it down:
- The Replace function replaces the string ‘Bearer ‘ with blank (including the space after)
- The Split function splits the token into the header, payload data, and signature parts of the JWT. We are interested in the payload, so refers to that with index [1]
split(replace(body('Parse_JSON_Headers')?['Authorization'], 'Bearer ',''), '.')[1]Now it becomes a little tricky. We will have to use the base64ToString function to get the payload into readable string, but if the length of the payload isn’t dividable by 4 we will get an error. Therefore we need to see if we need to add padding (=), as explained here: (Base64 – Wikipedia).
First I get the length of the payload data, and then use modulo function to see if there are any remaining data after dividing by 4:
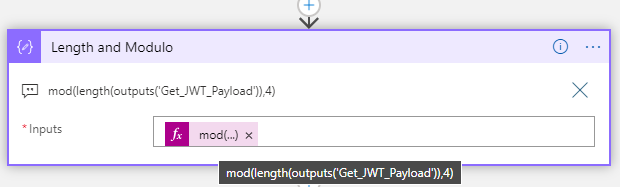
mod(length(outputs('Get_JWT_Payload')),4)Then I can do a conditional logic, where I use concat to add padding (=) to make it dividable by 4:
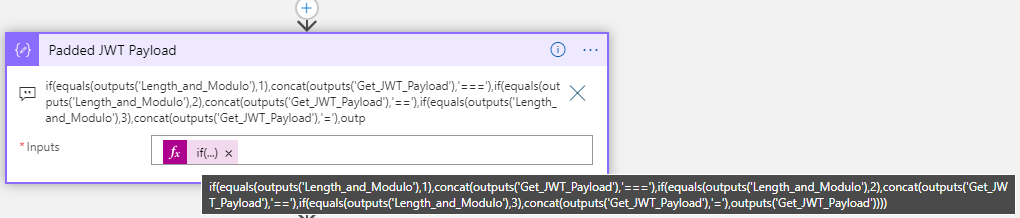
if(equals(outputs('Length_and_Modulo'),1),concat(outputs('Get_JWT_Payload'),'==='),if(equals(outputs('Length_and_Modulo'),2),concat(outputs('Get_JWT_Payload'),'=='),if(equals(outputs('Length_and_Modulo'),3),concat(outputs('Get_JWT_Payload'),'='),outputs('Get_JWT_Payload'))))After this I can use base64ToString to convert to a readable string object and format to JSON object:
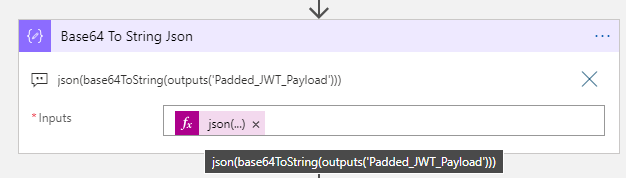
json(base64ToString(outputs('Padded_JWT_Payload')))Now that we have access to the claims, we can later be able to do some authorization in the Logic Apps, for example based on roles or scopes, but we can also get some information on which user that has called the Logic App.
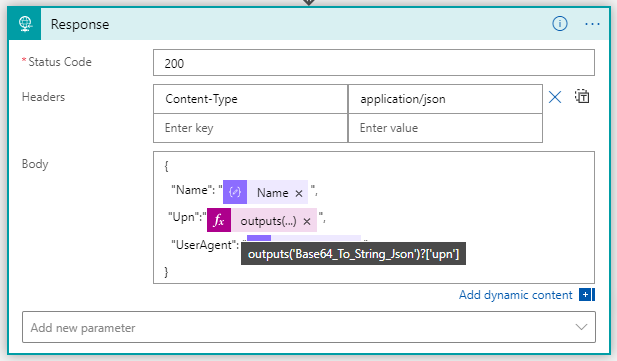
In the Response action, add the following to return the Name claim:
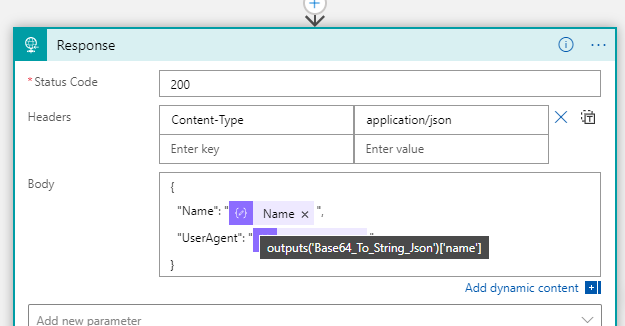
And if I test the Logic App http request again, I can see at it indeed returns my name based on the claims from the access token:
We now have a way to identify users or principals calling the Logic App. The Authorization Policy for the Logic App now permits users and principals from my own organization (based on the issuer claim) and as long as the audience is for management.core.windows.net. But what if I want external access as well? Let’s add to the authorization policies next.
Add OAuth Authorization Policy for Guests
A logic app can have several Azure AD Authorization Policies, so if I want to let external guest users to be allowed to trigger the logic app, I will need to create another authorization policy that allows that issuer:
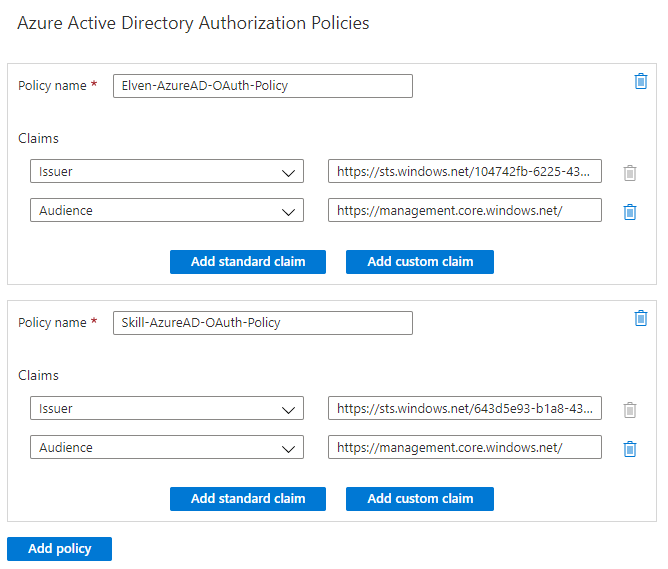
Lets also add the upn claim to the response, so it is easier to see which user from which tenant that triggered the Logic App:
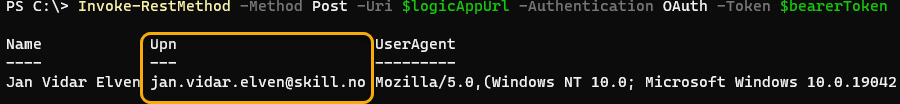
When I now test with different users, internal to my tenant and external, I can see that it works and the response output is as expected:

Summary of Management Access Scenarios
The purpose of the above steps has been to provide a way for management scenarios, where users and principals can get an Access Token using one of the Azure Management well known endpoints, and provide that when calling the Logic App. The access token is validated using OAuth Authorization Policies, requiring specific issuer (tenant id) and audience (management endpoint). This way we can make sure that we don’t have to share the SAS details which lets users that have access to this URL call the Logic App without authentication.
In the next parts of this blog post articles, we will look into more advanced scenarios where we will expose the Logic App as an API and more.